Network
virtualization in Windows Server 2012 is one of my favorites, because it’s just
so technical and revolutionary for the entire industry.
I have
blogged about both network
virtualization in VMM SP1 (CTP2) before, and
the extensible switch in Hyper-V.
It’s
important to know that there’s several new features and options in System
Center – Virtual Machine Manager 2012 SP1 – BETA related to network
virtualization, so I will start to blog about it now and walk through the
different configuration options.
This
blog post will talk about the networking Fabric.
Fabric
in VMM is a layer of abstraction above your physical and virtual infrastructure
that should serve the purpose of cloud computing. Fabric will contain
virtualization hosts, networks and network equipment, storage, and also some
additional server roles that will maintain and support the life cycle of your
fabric resources.
When you
are configuring and deploying a Microsoft Private Cloud, Fabric in VMM is the
place to start.
Network
virtualization in VMM does also has its starting point here.A logical network in VMM can contain several sites, subnets and VLANs that represents the physical network.
Each
virtualization host must be physically connected and associated to the proper
logical network before you continue with network virtualization. Check this
blog post I wrote earlier about networking in VMM.
A
logical network must be in place as it’s the foundation for network
virtualization (CA’s and PA’S), no matter what kind of network virtualization
technique you are using.
Default in SP1 is NVGRE – and not IP-rewrite as in CTP2.
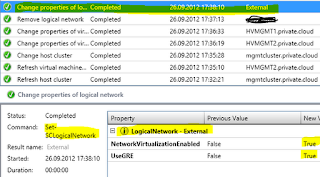
When you
enable networking virtualization on the logical network, you can see the
following in the jobs pane:
And during
this modification you’ll find an interesting agent installed on your Hyper-V
hosts:
More on
this in the next post.
Now, let’s
check what the Beta bits are bringing to the table.
Logical Switch
The
Hyper-V Extensible Switch is dramatically changed in Windows Server 2012
(previously known as networks) and
VMM fully supports and leverage its capabilities. An extensible virtual switch
provides several options and configurations in a natively fashion, and does
also supports ‘add-ons’ from thir-parties.
A
logical switch is meant to represent a single configuration for you to apply to
many or every hosts for a consistent configuration in your cloud infrastructure
fabric.Included in the logical switch is Native port profiles for uplink ports – used to define logical network definitions that should be available on every physical NIC connected to the logical switch.
Native port profiles for virtual ports – are used to define settings to
the virtual switches that your VMs are connected to.
Port classifications – works as an identity to classify
virtual port profiles for particular networks. So a VM can be deployed to
different logical switches where the name matches based on the virtual port
profiles on each switch.
More to
come in the near future.
-kn